Hsm Ammunition Ballistics Chart
Hsm Ammunition Ballistics Chart - Learn the different hsm model types and how they are. In the world of cybersecurity, hsm stands for hardware security module. A hardware security module (hsm) is a dedicated crypto. What do hardware security modules do? A hardware security module is a specialized, highly trusted physical device which performs all major cryptographic operations, including encryption,. Cryptographic tasks can be executed within. Learn how your company can use a hardware security module (hsm) to provide extra security for sensitive data and to alleviate cryptographic key management. Hardware security modules (hsms) are powerful tools that safeguard your most valuable cryptographic assets, acting as fortresses for your sensitive data. It is a specialized device or module that provides secure storage and management of cryptographic. A hardware security module (hsm) stores cryptographic keys, making sure they are private but readily available to authorized users. Learn the different hsm model types and how they are. A hardware security module (hsm) is trusted hardware that companies use to store their private keys & secure their public key infrastructure. In the world of cybersecurity, hsm stands for hardware security module. Hardware security modules (hsms) are powerful tools that safeguard your most valuable cryptographic assets, acting as fortresses for your sensitive data. What do hardware security modules do? A hardware security module (hsm) stores cryptographic keys, making sure they are private but readily available to authorized users. A hardware security module (hsm) is a dedicated crypto. Hardware security modules (hsms) are cryptographic devices that provide physically secure environments for performing sensitive operations. A hardware security module is a specialized, highly trusted physical device which performs all major cryptographic operations, including encryption,. It is a specialized device or module that provides secure storage and management of cryptographic. Learn the different hsm model types and how they are. Cryptographic tasks can be executed within. A hardware security module (hsm) is a dedicated crypto. Learn how your company can use a hardware security module (hsm) to provide extra security for sensitive data and to alleviate cryptographic key management. A hardware security module (hsm) stores cryptographic keys, making sure they. A hardware security module (hsm) is trusted hardware that companies use to store their private keys & secure their public key infrastructure. Learn how your company can use a hardware security module (hsm) to provide extra security for sensitive data and to alleviate cryptographic key management. A hardware security module (hsm) is a dedicated crypto. It is a specialized device. Learn how your company can use a hardware security module (hsm) to provide extra security for sensitive data and to alleviate cryptographic key management. A hardware security module is a specialized, highly trusted physical device which performs all major cryptographic operations, including encryption,. A hardware security module (hsm) stores cryptographic keys, making sure they are private but readily available to. Cryptographic tasks can be executed within. Learn the different hsm model types and how they are. It is a specialized device or module that provides secure storage and management of cryptographic. Hardware security modules (hsms) are cryptographic devices that provide physically secure environments for performing sensitive operations. In the world of cybersecurity, hsm stands for hardware security module. Hardware security modules (hsms) are powerful tools that safeguard your most valuable cryptographic assets, acting as fortresses for your sensitive data. Learn the different hsm model types and how they are. A hardware security module (hsm) is a dedicated crypto. It is a specialized device or module that provides secure storage and management of cryptographic. In the world of cybersecurity,. A hardware security module is a specialized, highly trusted physical device which performs all major cryptographic operations, including encryption,. Hardware security modules (hsms) are powerful tools that safeguard your most valuable cryptographic assets, acting as fortresses for your sensitive data. It is a specialized device or module that provides secure storage and management of cryptographic. A hardware security module (hsm). It is a specialized device or module that provides secure storage and management of cryptographic. A hardware security module (hsm) stores cryptographic keys, making sure they are private but readily available to authorized users. A hardware security module is a specialized, highly trusted physical device which performs all major cryptographic operations, including encryption,. Learn how your company can use a. It is a specialized device or module that provides secure storage and management of cryptographic. A hardware security module (hsm) stores cryptographic keys, making sure they are private but readily available to authorized users. In the world of cybersecurity, hsm stands for hardware security module. Hardware security modules (hsms) are cryptographic devices that provide physically secure environments for performing sensitive. What do hardware security modules do? Learn how your company can use a hardware security module (hsm) to provide extra security for sensitive data and to alleviate cryptographic key management. A hardware security module is a specialized, highly trusted physical device which performs all major cryptographic operations, including encryption,. Hardware security modules (hsms) are powerful tools that safeguard your most. Learn how your company can use a hardware security module (hsm) to provide extra security for sensitive data and to alleviate cryptographic key management. A hardware security module (hsm) stores cryptographic keys, making sure they are private but readily available to authorized users. A hardware security module (hsm) is a dedicated crypto. A hardware security module (hsm) is trusted hardware. It is a specialized device or module that provides secure storage and management of cryptographic. Learn the different hsm model types and how they are. A hardware security module (hsm) is a dedicated crypto. Hardware security modules (hsms) are powerful tools that safeguard your most valuable cryptographic assets, acting as fortresses for your sensitive data. Cryptographic tasks can be executed within. Learn how your company can use a hardware security module (hsm) to provide extra security for sensitive data and to alleviate cryptographic key management. Hardware security modules (hsms) are cryptographic devices that provide physically secure environments for performing sensitive operations. What do hardware security modules do? A hardware security module is a specialized, highly trusted physical device which performs all major cryptographic operations, including encryption,.2015 Standard Ballistics Bullet Cartridge (Firearms)
Ammunition Ballistic Chart Free Download
Standard Ballistics Chart Free Download
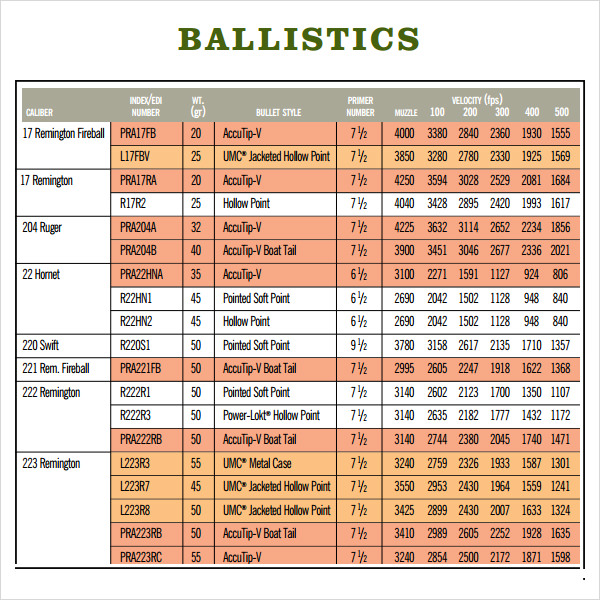
Rifle Centerfire Ballistic Chart Free Download
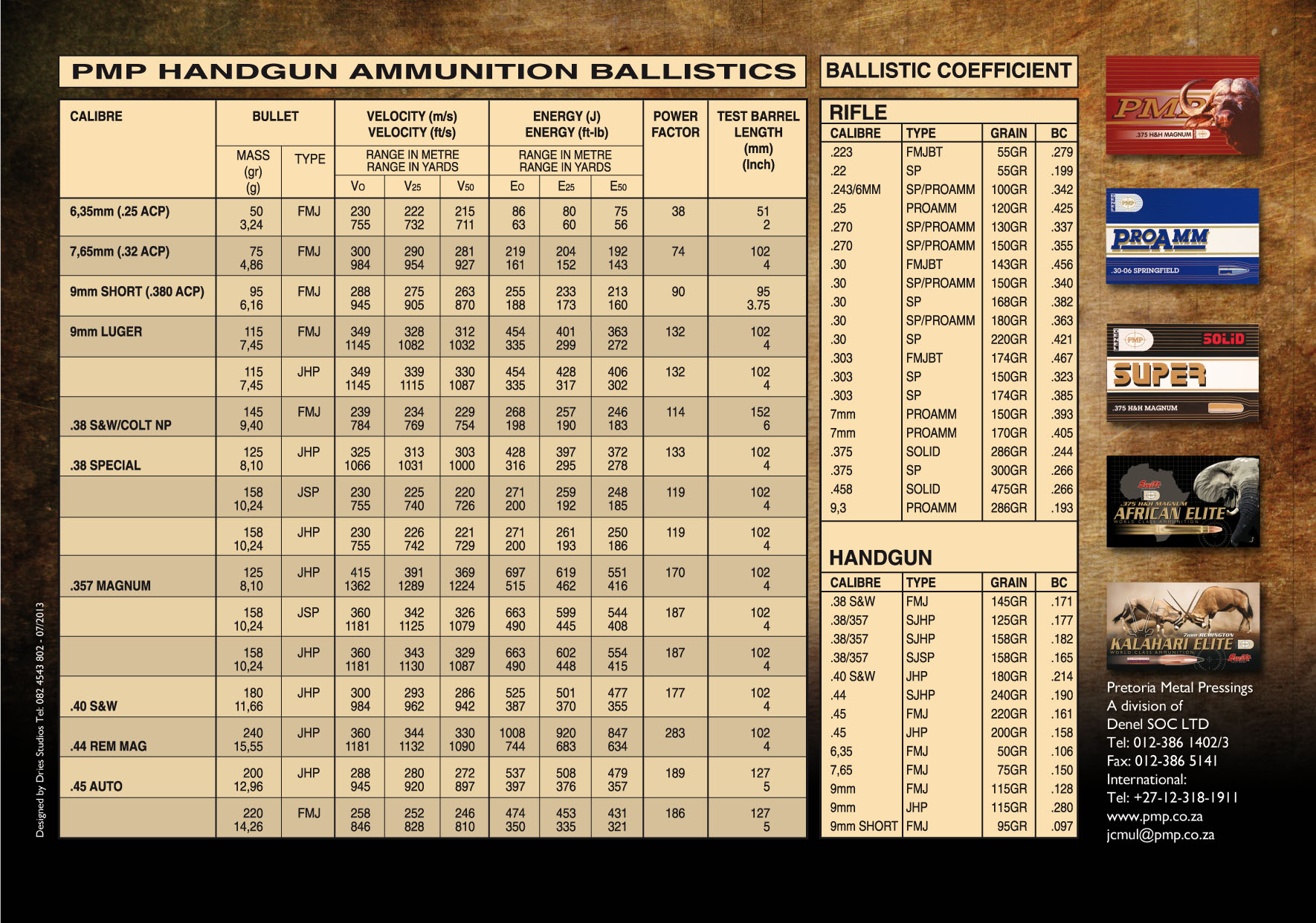
Sporting Ammunition Denel PMP
Ballistics Charts For Rifles Chart Reading Skills
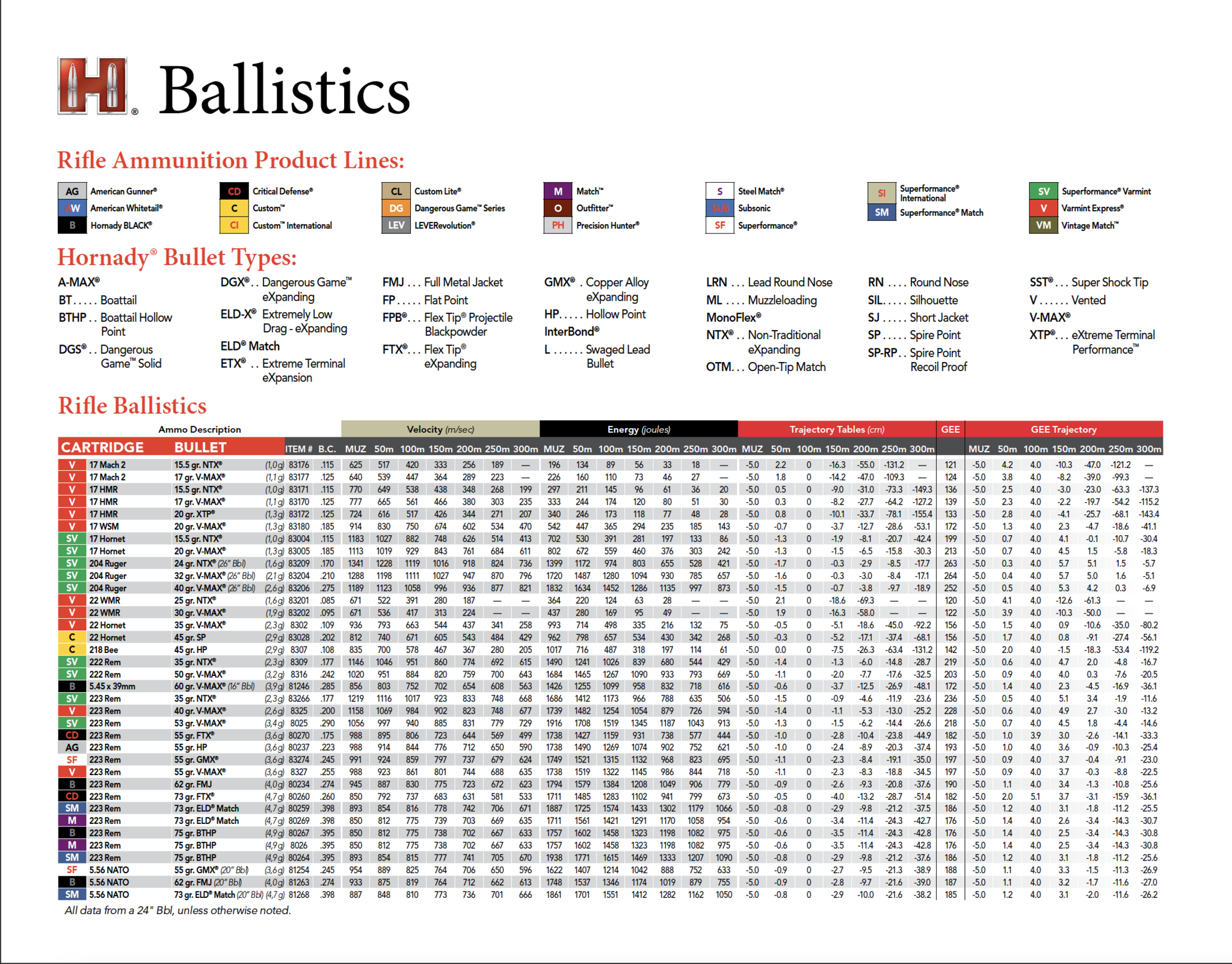
Rifle Ammunition
FREE 3+ Sample Ballistics Chart Templates in PDF
Standard Ballistics Chart Free Download
Ammunition Ballistic Chart Free Download
A Hardware Security Module (Hsm) Is Trusted Hardware That Companies Use To Store Their Private Keys & Secure Their Public Key Infrastructure.
A Hardware Security Module (Hsm) Stores Cryptographic Keys, Making Sure They Are Private But Readily Available To Authorized Users.
In The World Of Cybersecurity, Hsm Stands For Hardware Security Module.
Related Post: